I am not a security expert, nor do I profess to be any sort of virus removal expert, but from time to time we all have to deal with their removal. A couple of my earlier articles relating to viruses seem to be popular so I thought I would share my latest conquest. Perhaps not the best method but it worked for me. This one reared its self as a popup warning with “S.M.A.R.T. Repair” and advised of hard drive issues. This is another variation of the “FakeAlert” virus that has been known over the last number of years as XP Security 2011, Security Shield, XP Antivirus 2010, MAC Security, and so on.

Generally best practice is to remove a drive and attach it to another computer for scanning or as a minimum boot to safe mode. However, we do not always have that luxury and often have to try to repair remotely such in this case….
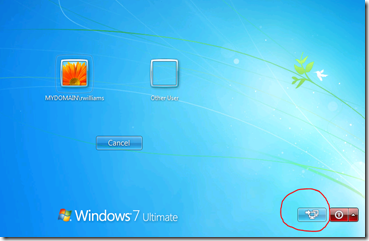
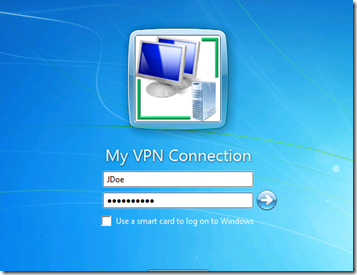
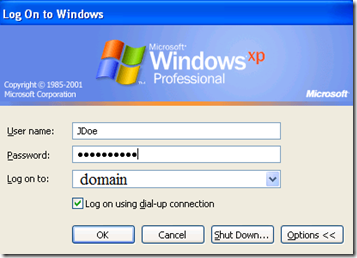
- My first step was to login as a different user than the one that was recently infected
Often the virus will not be active within another user’s profile, at least not until triggered. The most common trigger being accessing the internet with a browser.
- Next I created an additional admin account as soon as possible
This may or may not be possible at this point depending on the virus, but when it becomes option I do so incase this account gets infected and I have to start over.
Most often I try to do a system restore right away. Though this will not completely remove a virus, often it will disable it to allow you to do a thorough clean up with tools like Malwarebytes, TDSSKiller, and other anti-malware apps. You may have only seconds to start system restore after logon before the virus gets up and running and disables it. In these cases you can add a shortcut to the All Programs / Start Up folder with the following path %systemroot%\system32\rstrui.exe so that it automatically starts at logon, then log off and back on. It seems in many cases if you can get to the second window of System Restore before the virus completes its ‘boot up sequence’ it will run. In other cases it is either completely disabled, or all restore points have been removed.
I had read this virus removes desktop items and program menu items and puts them in a temp folder. In this case do not use a temp file cleaner and not knowing where or how the files were stored, I didn’t want to use System Restore.
- Next step was to copy Malwarebytes from a network share, and run.
Do not use a browser on the infected PC to download Malwarebytes as the browser will often trigger installation of the virus in the current user profile. I usually at this point run it in “Quick Scan” mode. There is a good chance this will kill the virus. It did so in my case, and does require a reboot.

- Upon reboot I ran TDSSKiller to check for any root kits.
In this case it was clean. The virus also had hidden many stem files and short cuts. For this,,,
- I use an application called “Unhide” which returned hidden files and shortcuts to a viewable state.
In some cases you may have to locate folders and manually unhide all files within the folder and subfolders using a command window and attrib -H *.* /S /D This virus also removed all personal desktop items, and all items within the folders of the Start Menu of the infected user. Based on the log file generated by Unhide, it may have restored these had I been logged in as the user when it was run.
Now logged in as the infected user, I was able to manually restore their missing desktop and Start Menu items by
- Copying the missing files from C:\Users\<infected user name>\AppData\Local\Temp\smtmp\1, & 4 to their appropriate locations
- I also had to manually add back start menu items such as My Music using the properties option of the task bar
- Next verify any existing anti-virus and/or anti-malware software is running, if not you may have to re-install
- Final step was to run a Malawrebytes “Full Scan” while logged in as the infected user.
All of this was performed remoty and apparently successful, but always remember “once infected, always suspected”. You can never be 100% sure the system is perfectly clean unless you do a full wipe and restore.
An excellent site for troubleshooting all types of viruses is bleepingcomputer.com and if interested in reading more about the FakeAlert viruses, and how you were infected see: “Stopping Fake Antivirus: How to Keep Scareware off Your Network“